Technology
90-9-1 Rule
1% Rule · Participation Inequality
90% of any given Internet community only view content, 9% edit, and 1% create. Said another way, 1% are participants while 99% are lurkers.
Amara's Law
The adage of overestimating the effect of a technology in the short run and underestimating the effect in the long run.
Automation Bias
The tendency to trust automated systems over one's own judgment or other information sources — accepting computer-generated recommendations even when contradictory evidence is available and correct.
Bathtub Curve
Used in reliability engineering, it describes a particular form of the hazard function (a type of failure) comprising three distinct parts — the first part is a decreasing failure rate known as early failures, the second a constant failure rate, known as random failures, and the third is an increasing failure rate, known as wear-out failures.
Betteridge's Law of Headlines
An adage holding that any news headline ending in a question mark can be answered by the word "no" — because if the answer were yes, the publisher would have stated it as fact.
Big Ball of Mud
In software, refers to a system with no recognizable structure or lacks a coherent architecture.
Black Box
A system or device whose inner workings are opaque and whose internal workings can only be guessed at through its inputs and outputs.
Bleeding Edge
The concept of technologies that are still untested or unstable and at the frontier of scientific and engineering development.
Bricolage
Construction or creation of a work from a diverse range of things that happen to be available, as opposed to strictly purpose-fabricated and planned.
Brooks' Law
The observation that adding more people to a late software project makes it even later, because new team members need ramp-up time and increase communication overhead.
Coding by Exception
A programming practice of handling each new edge case by adding special-case code rather than rethinking the underlying design. Quick to write, painful to maintain.
Copy and Paste Programming
Copying (and modifying) existing code rather than creating custom-fit solutions — can be used as a positive or negative.
Critical Path
The longest unbroken chain of sequential tasks or activities where delays along that path directly affect the overall completion time of the more general objective.
Cunningham's Law
"The best way to get the right answer on the Internet is not to ask a question, it's to post the wrong answer." The observation that people are quicker to correct a wrong answer than to answer a question.
Dependency Inversion Principle
Software design principle that advocates for high-level modules to depend on abstractions, rather than on low-level modules, to allow for flexibility, maintainability, and scalability of the system.
Development Cycle
SDLC · Software Development Life Cycle
In software, the process of dividing software development work into distinct phases to improve design and project management. Current methodologies include agile, waterfall, prototyping, iterative and incremental development, spiral development, rapid application development, and extreme programming.
Diffusion of Innovation
The theory explaining how new ideas and technologies spread through a population — from early adopters to the mainstream to the laggards.
Driveway Moment
The act of staying in one's car or hesitating to enter one's destination even after arriving due to being engrossed in a podcast or radio story and wanting to reach a stopping point.
Error Hiding
Diaper Pattern · Pokemon Exception Handling
In computer programming, the practice of 'catching' an error message before it can be shown to the user and either showing nothing or showing a meaningless message.
Every Fool their own Tool
A phenomenon where software developers fail to use proper software development principles when creating tools — often to facilitate the software development process itself.
Filter Bubble
The notion that users get less exposure to conflicting viewpoints and are isolated intellectually in their own informational bubble, particularly on social media platforms.
Fly-by-Wire
FBW
In aviation, a system that replaces the conventional manual flight controls of an aircraft with an electronic interface.
Godwin's Law
Godwin's Rule of Nazi Analogies
The observed Internet phenomenon where if an online discussion (regardless of topic or scope) goes on long enough, sooner or later someone will compare someone or something to Hitler or Nazism.
Google Effect
Digital Amnesia
The tendency to forget information that can be found readily online by using Internet search engines such as Google.
Halting Problem
In computing, the challenge in determining just from code and an input, whether the program will actually finish (halt), or continue to run forever.
Hard Code Vs. Soft Code
Embedding data directly into the source code of a system, whereas 'soft code' embeds data in external locations or configuration files. These two coding practices have tradeoffs of time to develop, scaling, and sustainability.
Hostile Media Effect
Hostile Media Phenomenon · Hostile Media Perception
A perceptual theory of mass communication that refers to the tendency for individuals with a strong pre-existing attitude on an issue to perceive media coverage as biased against their side and in favor of their antagonists' point of view.
Hype Cycle
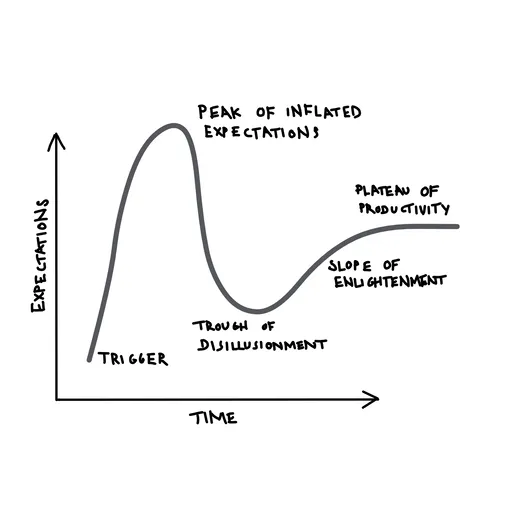
The experience of any new technology over time where its inception generates inflated hype, followed in turn by disillusionment, and finally back up to a renewed but realistic opportunity.
Ikea Effect
The exaggeratedly high value and attachment placed on products that one builds themselves, regardless of the end result quality.
Impedance Matching
The practice, in electronics, of designing the input impedance of an electrical load or the output impedance of its corresponding signal source to maximize the power transfer or minimize signal reflection from the load.
Inner-Platform Effect
A system built within an existing platform (due to constraints, preferences, etc.) that has become so complex that it has become a poor replica of an existing platform.
Intentionality Fallacy
Intentional Fallacy
The insistence that the ultimate meaning of an expression must be consistent with the intention of the person from whom the communication originated. For example, a work of fiction that is widely received as a blatant allegory must necessarily not be regarded as such if the author intended it not to be so.
Interface Segregation Principle
ISP
A software design rule holding that no client should be forced to depend on methods it does not use — large interfaces should be split into smaller, more specific ones so each client only knows about what it needs.
Inversion of Control
Hollywood Principle
A software design principle where a framework calls your code, rather than your code calling the framework. Often summarized as "don't call us, we'll call you."
Jevon's Paradox
Jevons paradox · Jevons effect · rebound effect · backfire effect
The observation that improvements in the efficiency of resource use often lead to increased total consumption of that resource rather than decreased consumption. As efficiency lowers the effective cost per unit, demand rises enough to offset or exceed the original savings.
Joy of Missing Out (JOMO)
Contrast with the Fear of Missing Out (FOMO), JOMO is the experience of relief, delight, and lack of anxiety associated with \*not\* participating in every and all activities that in particular are captured and shared via social media.
Knoll's Law of Media Accuracy
"Everything you read in the newspapers is absolutely true — except for that rare story of which you have firsthand knowledge." A wry reminder that media accuracy looks different from the inside.
Lasagna Code
Software with too many layers of abstraction stacked on top of each other, making it difficult to understand or modify any single piece.
Lava Flow
Dead Code
Retaining undesirable code because removing it is too expensive or has unpredictable consequences.
Lindy Effect
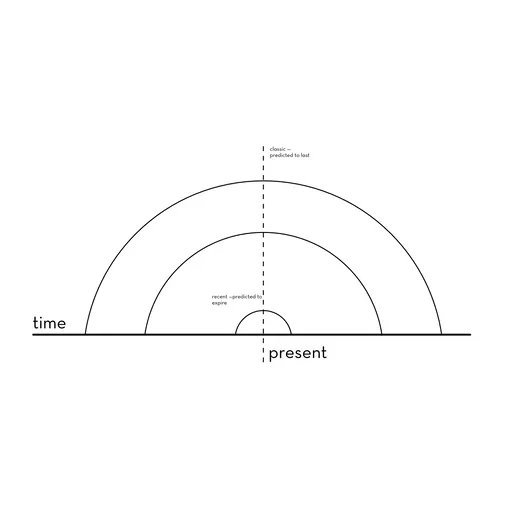
The idea that the future life expectancy of some non-perishable things like a technology or an idea is proportional to their current age, so that every additional period of survival implies a longer remaining life expectancy.
Liskov Substitution Principle
A software design principle holding that objects of a superclass should be replaceable with objects of a subclass without altering the correctness of the program.
Magic Strings
Implementing presumably unlikely input scenarios, such as comparisons with very specific strings, to mask functionality.
Medium is the Message
The form of a medium embeds itself in any message it would transmit or convey, creating a symbiotic relationship by which the medium influences how the message is perceived.
Minimum Viable Product
A product that has been targeted to be built with just enough features to gather validated learning about the product and its continued development and no more.
Moore's Law
The observation that the number of transistors in a dense integrated circuit doubles approximately every two years — an empirical trend that has held for decades and driven exponential growth in computing power.
Moravec's Paradox
An observation in artificial intelligence research that high-level reasoning requires relatively little computation, while low-level sensorimotor skills like perception and mobility demand enormous computational resources.
Mosaic Effect
Separate pieces of information, that by themselves have limited usability, become important and/or revealing when combined. Of particular importance in digital confidentiality and privacy.
Ninety-Ninety Rule
90-90 Rule
The adage, often in computer programming, that the first 90 percent of the code in a project accounts for the first 90 percent of the development time, and the remaining 10 percent of the code accounts for the other 90 percent of the development time. In other words, the tendency to underestimate the amount of time to complete a project when it is "nearly done".
Not Invented Here
NIH Syndrome
The tendency for organizations towards reinventing the wheel rather than adopting and adapting an existing, adequate solution.
Novelty Effect
The tendency for performance to initially improve when new technology is instituted, not because of any actual improvement in learning or achievement, but in response to increased interest in the new technology.
Off-By-One Error
Programming mistake that occurs when a programmer incorrectly references or iterates through an array or loop, resulting in the code either skipping over or repeating one element.
Open-Closed Principle
Software design principle that states that software entities should be open for extension but closed for modification, meaning that they should be designed in a way that allows for easy addition of new functionality without changing the existing code.
Overengineering
Building something far more complex or robust than the situation requires. The extra effort adds cost and rigidity without meaningful benefit.
Planned Obsolescence
Built-In Obsolescence
A policy of planning or designing a product with an artificially limited useful life, so it will become obsolete (that is, unfashionable or no longer functional) after a certain period of time.
Premature Optimization
The notion from computer science that one should not spend an inordinate amount of time trying to optimize or refactor code prior to understanding where it becomes clear where the bottlenecks and slowdowns are going to be.
Pro-Innovation Bias
The assumption that all innovations are inherently beneficial and should be rapidly adopted by everyone in a social system, often ignoring potential disadvantages, risks, or the need for modification.
Programming by Permutation
Programming by Accident · Programming by Coincidence
Trying random changes to code until something works, without understanding why. Sometimes called "trial and error debugging" — effective by accident, fragile by nature.
Red Pill Vs. Blue Pill
The red pill and its opposite, the blue pill, are a popular cultural meme, a metaphor representing the choice between knowledge, freedom, uncertainty and the brutal truths of reality (red pill), and then security, happiness, beauty, and the blissful ignorance of illusion (blue pill).
Revenge Effect
When a technology produces the opposite effect of its intended purpose, such as antibiotics that breed resistant bacteria or security systems that generate so many false alarms they reduce actual vigilance.
Rubber Ducking
Rubber Ducking
A debugging method in software development where a programmer explains their code line-by-line to an inanimate object, such as a rubber duck, to identify errors through the process of articulation.
Sambaza
In Western Kenya, it means "to spread", and refers to marketing slogans for mobile connectivity, as well as to refer to the way money slips away, drip by drip, as friends and family ask for favors.
Self-Replicating Programs
Quines
A non-empty computer program which takes no input and produces a copy of its own source code as its only output.
Separation of Concerns
Software engineering principle that emphasizes the importance of dividing a system or application into distinct and modular components, with each component addressing a specific concern or aspect of the system.
Shotgun Surgery
A code smell where a single change requires making many small edits scattered across multiple files or modules. A sign of poor separation of concerns.
Single Responsibility Principle
Software design principle that states that a class or module should have only one reason to change, and should be responsible for only one aspect or feature of the system it represents.
Smoke and Mirrors
Demonstrating features or characteristics in a disingenuously glossy or finished state as if they were already implemented.
Software is Eating the World
The idea that software companies are disrupting and transforming entire industries beyond traditional tech, reshaping the broader economy and culture.
Streisand Effect

The phenomenon where an attempt to hide, remove, or censor a piece of content has the unintended consequence of drawing more attention to that content.
Tamagotchi Effect
The tendency to form emotional attachments to machines, robots, or software — caring for digital things as if they were alive.
Technology Adoption Lifecycle
Diffusion of Innovations · Rogers' Curve
The adoption or acceptance of a new product or innovation, according to the demographic and psychological characteristics of defined adopter groups. The first group are called ‘innovators', followed by ‘early adopters', 'early majority' and 'late majority', and finally ‘laggards'.
Tester-Driven Development
A (usually unintentional) software practice where new requirements emerge through bug reports rather than upfront planning. The testers end up defining the product.
The Singularity
Technological Singularity
The idea that the invention of artificial intelligence will trigger runaway technological developments, that compounds on itself, which would result in unpredictable changes to human civilization.
Third-Person Effect
The notion that people perceive that mass media messages have a greater effect on others than on themselves.
Threat Detection
In computer security, a threat is a possible danger that might exploit a vulnerability to breach security and therefore cause possible harm.
Turboencabulator
A fictional machine described in dense, authoritative-sounding nonsense, used as a long-running engineering in-joke to parody impenetrable technical jargon.
Turing Test
A test of a machine's ability to exhibit intelligent behavior equivalent to, or indistinguishable from, that of a human.
Uncanny Valley
The increasing unease one experience as an entity approaches realistic humanoid characteristics or appearance, where the more realist (but still subtly not human) the entity appears, the greater unease or cold feelings are felt, where if the entity is decidedly not humanoid then we experience little unease.
Vaporware
A product, typically computer hardware or software, that is announced to the general public but is never actually manufactured nor officially cancelled.